This paper presents a groundbreaking framework for device-independent quantum key distribution (DIQKD) security analysis using semidefinite programming. DIQKD represents the most secure form of key exchange, requiring only input-output statistics rather than trusted devices. While previous security proofs were limited to specific scenarios like CHSH inequality violations, this new approach offers a universal method for calculating secret key rates in any DIQKD protocol.
The core innovation is a computational toolbox that directly calculates von Neumann entropy bounds using complete measurement statistics. This advancement is significant because earlier approaches either required reduction to qubit-level systems or relied on min-entropy bounds, both of which had limitations. The qubit reduction method only worked for protocols with binary inputs and outputs, while min-entropy bounds typically produced suboptimal results for von Neumann entropy calculations, which are crucial for determining secret key rates against general attacks in the asymptotic limit.
The framework’s foundation lies in estimating entropy production in quantum channels acting on unknown states under algebraic constraints. Entropy production, traditionally associated with non-equilibrium thermodynamics, is shown to have fundamental connections to quantum cryptography. In the context of DIQKD, it represents the entropy difference between post-measurement and initial systems.
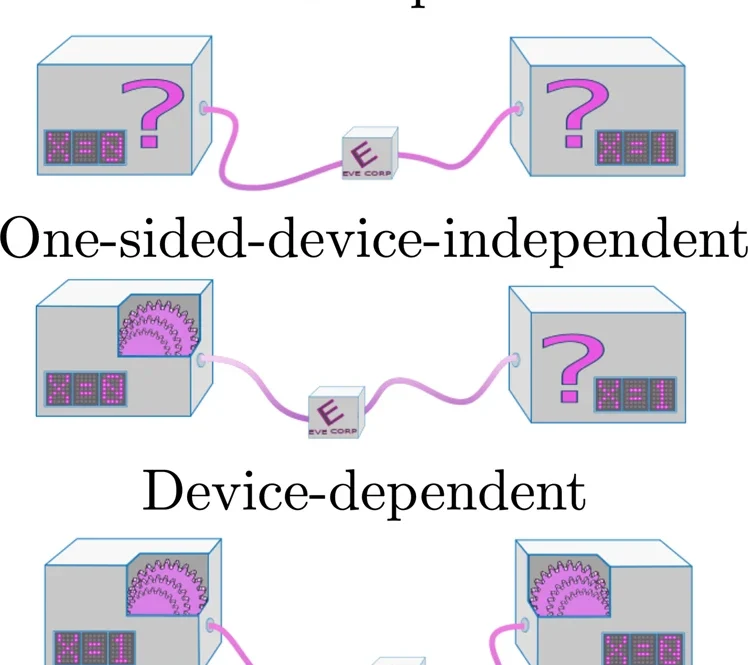
The method employs polynomial optimization over measurement operators, evaluated using semidefinite programming within the Navascués-Pironio-Acín (NPA) hierarchy. This approach is remarkably versatile, extending beyond DIQKD to other device-independent cryptographic tasks like randomness expansion. It can adapt to varying levels of device characterization, from fully device-independent to device-dependent scenarios, with additional constraints in the semidefinite programming leading to higher secret key rates.
This framework’s significance lies in its ability to analyze more complex scenarios than previously possible, including non-standard protocols known for better noise and loss resistance, as well as multipartite protocols. The method relies on nonlocal correlations, typically measured through Bell inequality violations, which certify that the key must originate from entangled state measurements. By providing a universal computational approach to security analysis, this work represents a significant advance in quantum cryptography, offering practical tools for analyzing a broader range of quantum communication protocols.
npj Quantum Information, Published online: 29 October 2021; doi:10.1038/s41534-021-00494-z