Despite significant theoretical and experimental advancements in Continuous Variable Quantum Key Distribution (CV QKD), rigorous security proofs for systems with practical imperfections remain underdeveloped compared to discrete variable approaches. This paper specifically addresses intensity fluctuation, which poses a major security challenge in CV QKD implementations.
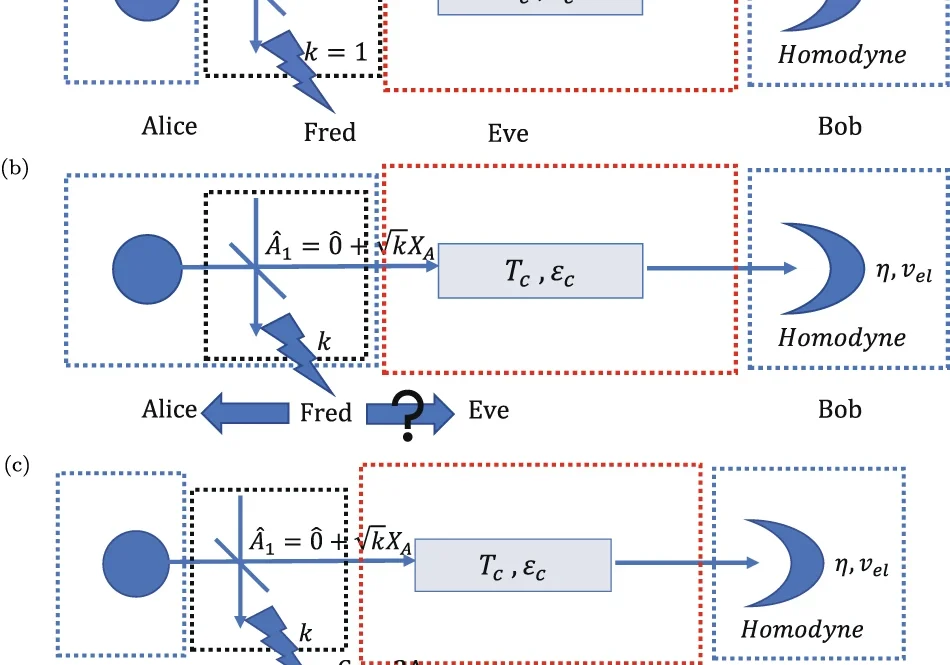
The authors present comprehensive security proofs for CV QKD systems affected by intensity fluctuations, categorizing scenarios based on whether Alice (the sender) can monitor these fluctuations. When Alice can track fluctuations, the proof integrates over their distribution and refines data analysis to improve performance over long distances. When Alice cannot monitor each pulse, two subcases emerge: either Eve (the eavesdropper) can monitor fluctuations, or neither party can.
For the case where Eve has access to fluctuation information but Alice doesn’t, the authors apply Gaussian extremality principles. In the most conservative scenario where neither Alice nor Eve can monitor each pulse, they adapt the “tagging” concept from discrete variable QKD. This approach divides signals into “tagged” and “untagged” categories based on whether their intensities fall within prescribed boundaries, allowing users to establish security bounds without needing to identify individual signal classifications.
Significantly, the authors demonstrate that their proofs enable secure key generation in finite-size scenarios over distances exceeding 50 kilometers. The proposed techniques require no hardware modifications to existing CV QKD systems, making them immediately implementable. This work bridges a critical gap in quantum cryptography by providing practical security assurances for realistic CV QKD implementations with imperfect sources.
npj Quantum Information, Published online: 14 October 2021; doi:10.1038/s41534-021-00482-3